
The signal in
the noise
High-impact summaries of the most critical vulnerabilities and emerging threats. The need-to-know intel that keeps your perimeter hardened.
This week's critical
threat briefing
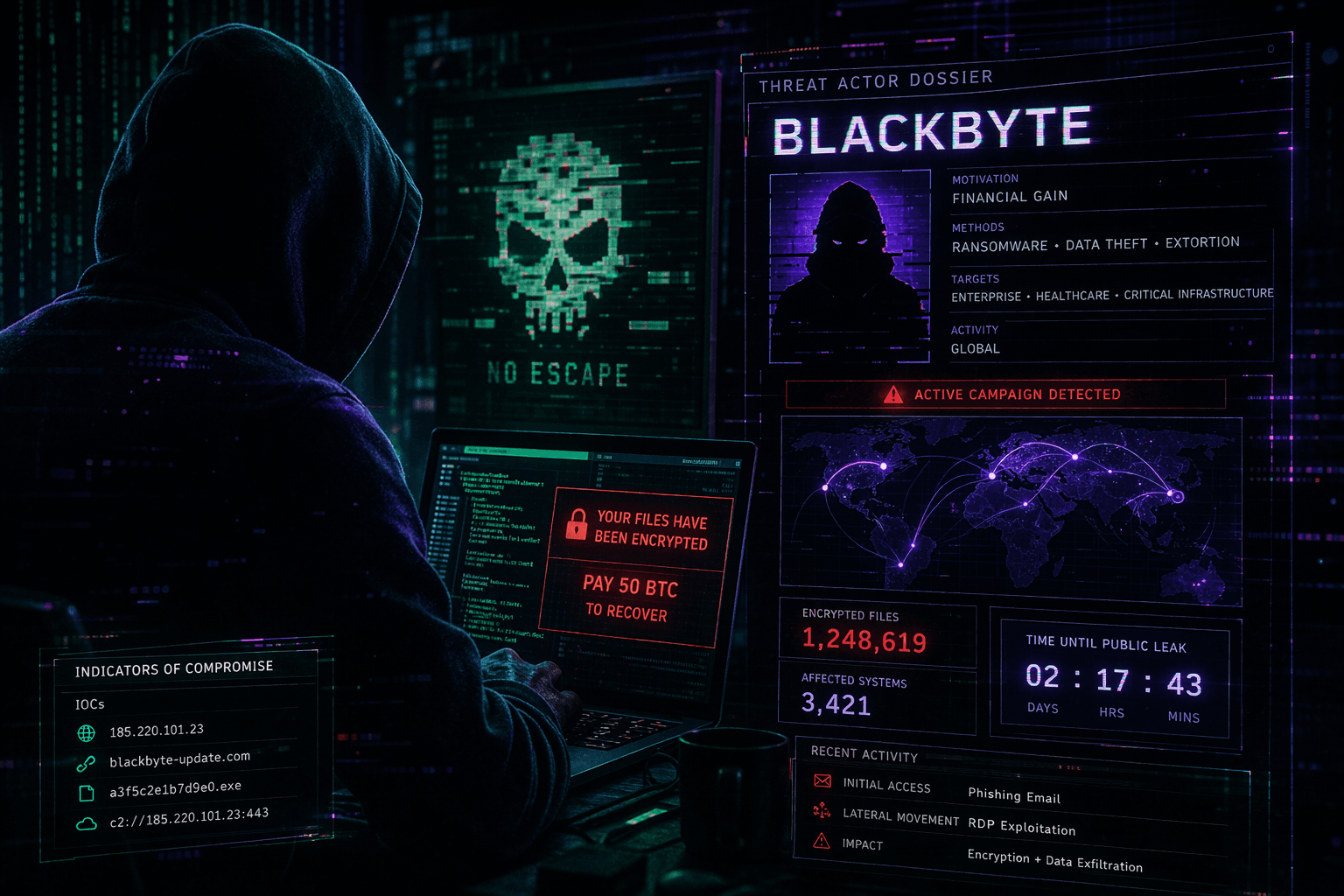
Qilin Found a Way to Blind Your EDR Before You Know They're Inside
Cisco Talos and Trend Micro confirm Qilin ransomware is using BYOVD to systematically disable 300+ EDR products before deploying ransomware. Here's the full attack chain and what to do about it.
Your threat landscape is
outpacing your team
Every day, new vulnerabilities emerge and threat actors move faster. The cost of missing a critical alert isn't just technical — it's existential.
Alert Overload
Your SIEM fires thousands of alerts daily. Critical CVEs get buried under noise. By the time your team triages, the window to patch has already closed.

Too Slow to React
Threat actors exploit within hours. Your intel pipeline takes days. The gap between disclosure and exploitation is shrinking — and you're on the wrong side of it.
Fragmented Intel
NVD, vendor advisories, Twitter, dark web forums — your analysts juggle dozens of sources. Context is scattered. Priority is guesswork.
Talent Shortage
The cybersecurity skills gap is real. Your lean team can't cover every advisory, every CVE, every threat campaign. Something always slips through.
Threat intel that cuts through
Decryption Digest distills the global threat landscape into actionable intelligence your team can act on immediately.
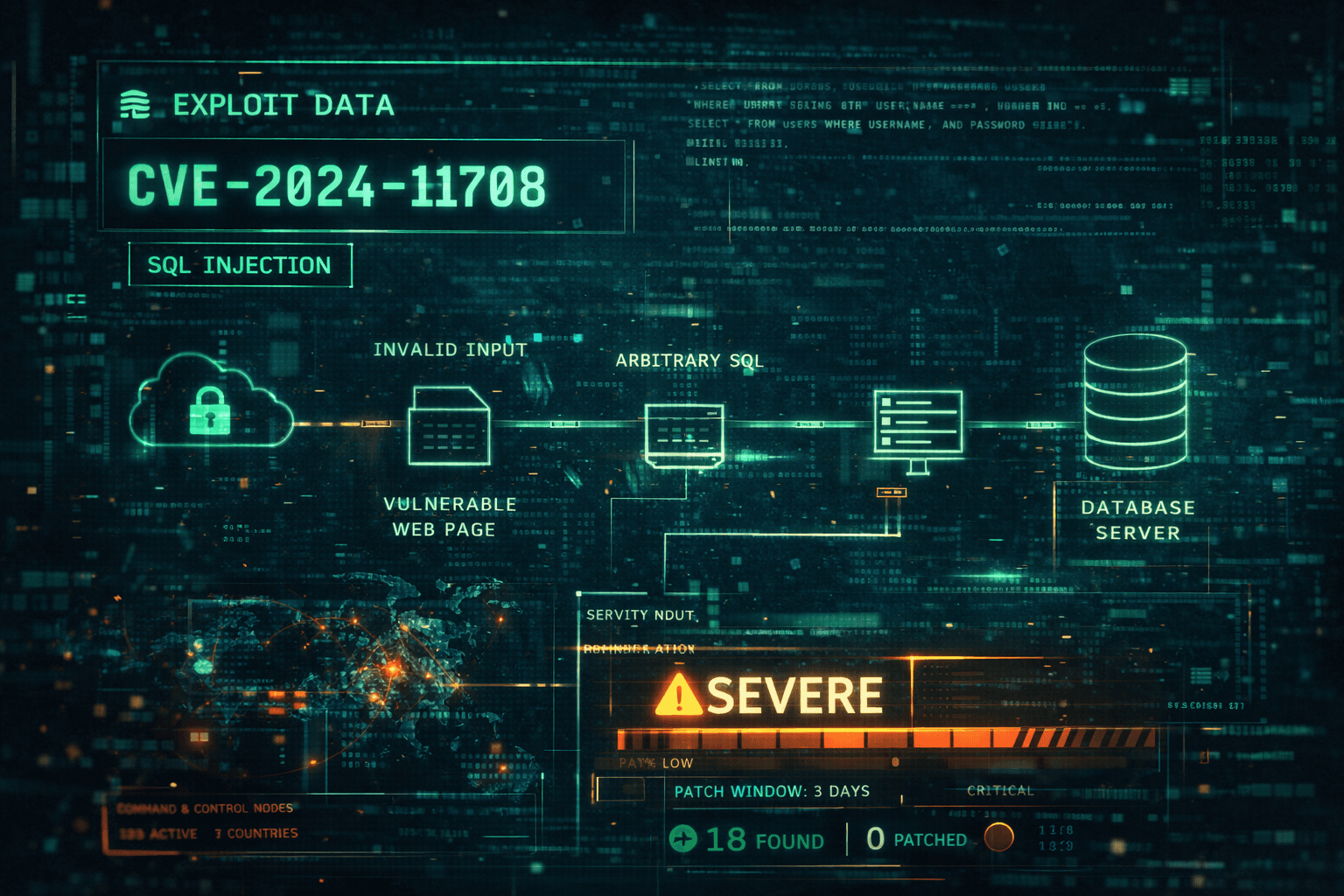
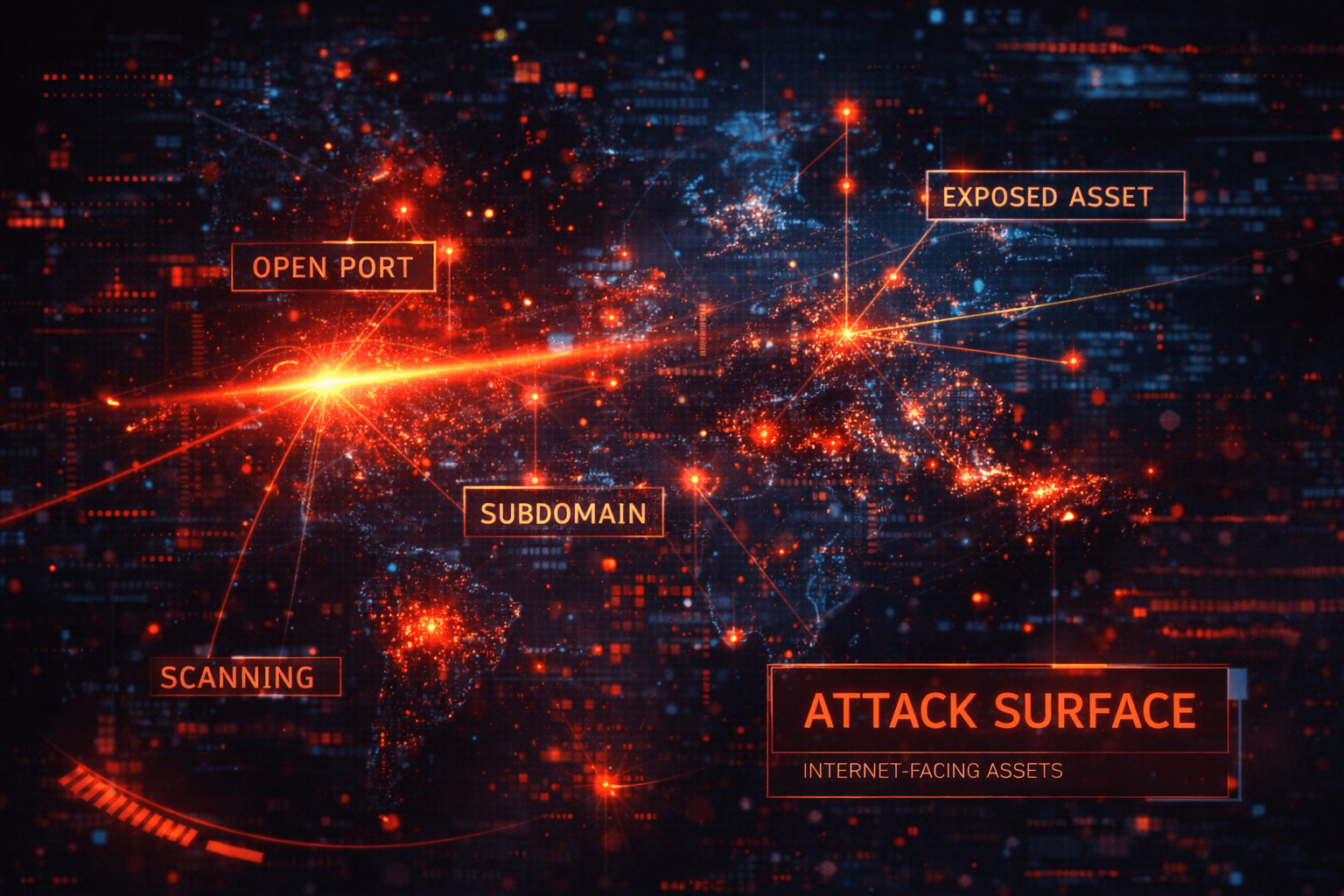
Sample Analysis — CVE Exploit Path Mapping
Curated, Not Automated
Every digest is reviewed for accuracy, relevance, and impact. No AI hallucinations. No recycled vendor marketing. Just verified threat intel.
Actionable Context
We don't just report CVEs — we tell you what's being actively exploited, who's targeted, and what to patch first. Remediation guidance included.
Real-Time Delivery
Critical alerts reach you within hours of disclosure — not days. Our monitoring pipeline covers NVD, vendor advisories, exploit databases, and dark web chatter.
Strategic Prioritization
CVSS scores don't tell the whole story. We factor in exploit maturity, threat actor activity, and your industry context to rank what matters most.
Concise by Design
No 40-page PDFs. Each digest is structured for fast consumption — scan in 5 minutes, act immediately. Built for busy security teams.
Zero Noise Guarantee
We only surface what's critical. If it's not actively exploited or doesn't pose imminent risk, it doesn't make the cut. Your inbox stays clean.
From chaos to clarity
in four steps
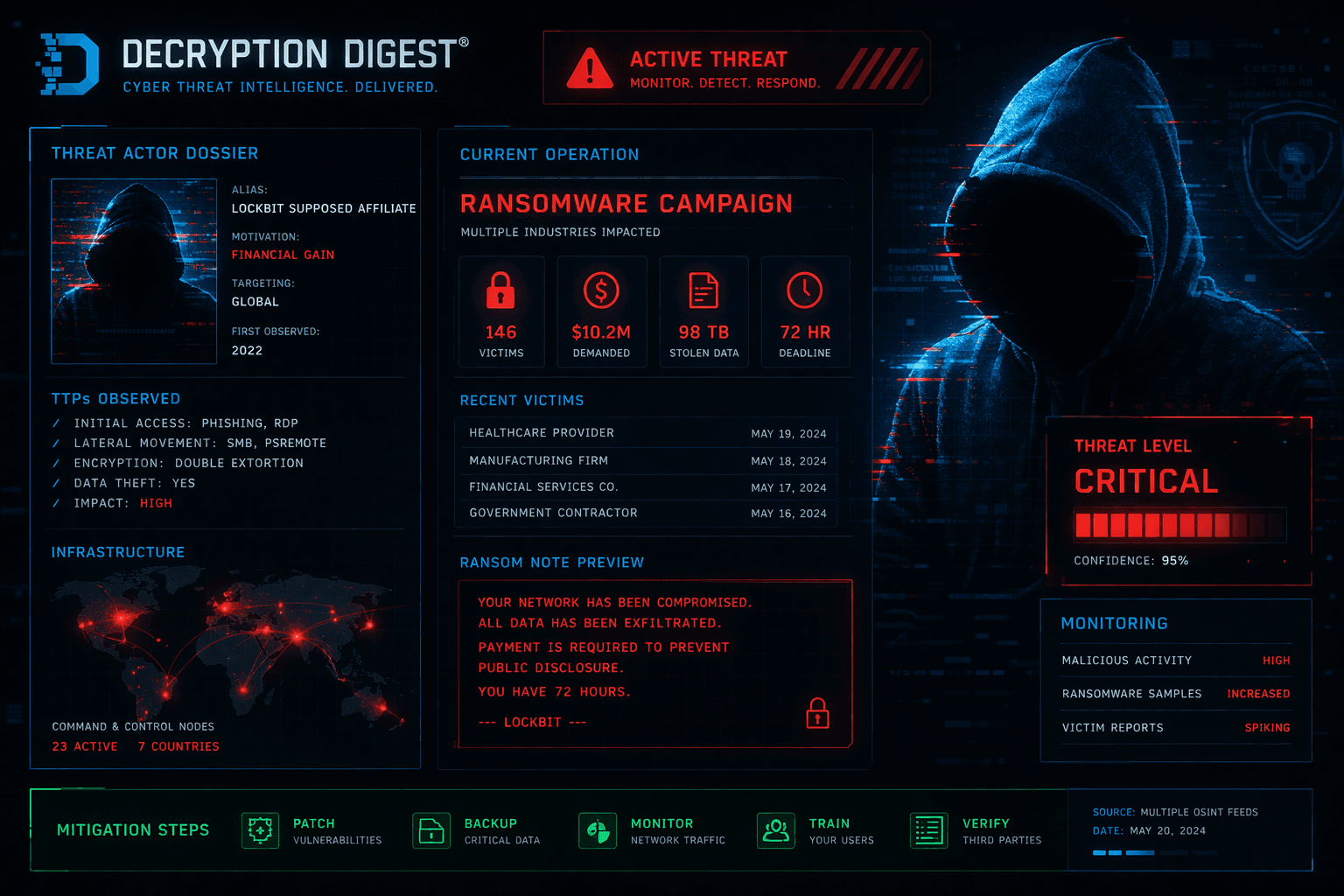
Digest Sample — Ransomware Campaign Analysis
LIVE PREVIEWWe Monitor Everything
Our pipeline ingests data from NVD, vendor advisories, exploit databases, threat feeds, and dark web sources — 24/7, around the clock.
We Filter the Noise
Automated triage paired with expert analysis. We evaluate exploit maturity, active campaigns, and real-world impact to surface only what matters.
We Deliver the Intel
You receive a concise, prioritized digest with CVE details, affected systems, threat context, and remediation steps — ready to act on.
You Stay Ahead
Your team patches what matters first, briefs leadership with confidence, and closes the gap between disclosure and defense.
Trusted by security teams
at every scale
Decryption Digest cut our mean time to remediate by 40%. We patch what matters first now, instead of chasing every advisory.
I used to spend 2 hours every morning triaging threat feeds. Now I spend 5 minutes reading the digest and my day starts with clarity.
The remediation context is what sets this apart. It's not just 'here's a CVE' — it's 'here's what to do about it and why it matters for your stack.'
Built by defenders,
for defenders
Decryption Digest was born from a simple frustration: security teams spending more time parsing intel than acting on it. Founded by veteran threat analysts and incident responders, we built the briefing we always wished we had.
Our team combines deep expertise in vulnerability research, threat hunting, and security operations. We've worked the SOC floors, led red teams, and managed enterprise security programs. We know what matters because we've lived it.
Stop reacting.
Start anticipating.
Join 50,000+ security professionals who start their day with the intelligence that matters. Free. No spam. Unsubscribe anytime.
Trusted by teams at Fortune 500 companies. No credit card required.